Setting up Google Authenticator MFA on Amazon Linux 2
Set up a Google Authenticator based TOTP MFA for your Amazon Linux 2 server.
Sometimes, the data in your servers are so valuable that having ssh key with passphrase, IP restrictions and sudo password all together won't just cut it for your organisation's security policy.
In this case, you'll have to set up MFA for your server, and following are the steps.
Here I am setting a Google Authenticator based MFA for Amazon Linux 2 in addition to a password based authentication for the user. You can use key based authentication also with small changes in configuration.
Installation of Google Authenticator
First, enable the epel repo in AL2
sudo amazon-linux-extras install epel -yNow you can install the google-authenticator package
sudo yum install google-authenticator -yCreating MFA
Now run the google-authenticator command and give the following responses
[ec2-user@vm_al2 ~]$ google-authenticator
Do you want authentication tokens to be time-based (y/n) y
Warning: pasting the following URL into your browser exposes the OTP secret to Google:
https://www.google.com/chart?chs=200x200&chld=M|0&cht=qr&chl=otpauth://totp/ec2-user@vm_al2%3Fsecret%3DKPPS2C44OQMUYKQCNEG45SVIL4%26issuer%3Dvm_al2

Your new secret key is: KPPS2C44OQMUYKQCNEG45SVIL4
Your verification code is 061304
Your emergency scratch codes are:
53063172
99973171
81062482
92606712
26718859
Do you want me to update your "/home/ec2-user/.google_authenticator" file? (y/n) y
Do you want to disallow multiple uses of the same authentication
token? This restricts you to one login about every 30s, but it increases
your chances to notice or even prevent man-in-the-middle attacks (y/n) y
By default, a new token is generated every 30 seconds by the mobile app.
In order to compensate for possible time-skew between the client and the server,
we allow an extra token before and after the current time. This allows for a
time skew of up to 30 seconds between authentication server and client. If you
experience problems with poor time synchronization, you can increase the window
from its default size of 3 permitted codes (one previous code, the current
code, the next code) to 17 permitted codes (the 8 previous codes, the current
code, and the 8 next codes). This will permit for a time skew of up to 4 minutes
between client and server.
Do you want to do so? (y/n) n
If the computer that you are logging into isn't hardened against brute-force
login attempts, you can enable rate-limiting for the authentication module.
By default, this limits attackers to no more than 3 login attempts every 30s.
Do you want to enable rate-limiting? (y/n) yConfiguring the server to use MFA
Now configure the PAM module to use Google Authenticator while logging in
sudo vim /etc/pam.d/sshdEdit the file to include the following line
auth required pam_google_authenticator.so nullokThe nullok allows the users without MFA configured to login without MFA. Only the users with MFA will be asked for an MFA. This can be removed once all the users in the server has set the MFA.
Now edit the sshd configuration to as for the OTP challenge
sudo vim /etc/ssh/sshd_configEdit the configuration to change the ChallengeResponseAuthentication to yes
ChallengeResponseAuthentication yesSince I'm configuring this for password authentication only and not ssh key authentication, my sshd_config file has PasswordAuthentication yes instead of the default PasswordAuthentication no
Now you can restart the sshd process
sudo systemctl restart sshdConclusion
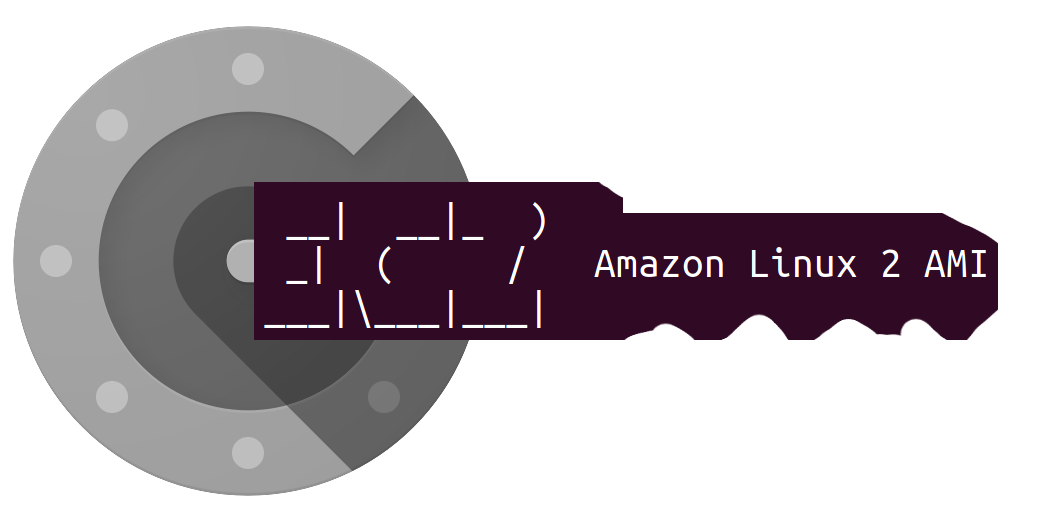
That's it, you can login with the MFA to your server
vignesh@workstation:~$ ssh ec2-user@192.168.122.125
Password:
Verification code:
Last login: Fri Apr 29 04:59:47 2022 from 192.168.122.1
__| __|_ )
_| ( / Amazon Linux 2 AMI
___|\___|___|
https://aws.amazon.com/amazon-linux-2/
55 package(s) needed for security, out of 95 available
Run "sudo yum update" to apply all updates.
[ec2-user@vm_al2 ~]$You can also copy the .google_authenticator file from your user's home folder to your local machine to keep the key, emergency use OTPs etc. safe.
[ec2-user@vm_al2 ~]$ cat .google_authenticator
KPPS2C44OQMUYKQCNEG45SVIL4
" RATE_LIMIT 3 30 1651209615
" DISALLOW_REUSE 55040320
" TOTP_AUTH
53063172
99973171
81062482
92606712
26718859Also if you want to use only key based authentication,
Open the pam file
sudo vim /etc/pam.d/sshdand comment the following line
#auth substack password-authReferences